What Are The Biometric Identification Technologies?
Biometric identification technologies are increasingly being used in various applications, ranging from security to personal identification. Biometric identification is the use of biological and behavioral characteristics as unique identifiers. The most common forms are fingerprints, face recognition, iris scans, voice analysis, and DNA. Biometric technology can be used in a number of fields – from healthcare to law enforcement.

Biometric identification is the use of biological and behavioral characteristics as unique identifiers.
It is the use of biological and behavioral characteristics as unique identifiers. Biometric identifiers are often used in security applications to verify identities, such as through fingerprint scanning or facial recognition software. Biometrics can be used for identification in many situations, including airports, hospitals, and schools.
It isn’t as accurate as other security systems. Because biometrics are measured differently for each person–and everyone’s body is slightly different from another’s–the data collected from one person might not match up with another person’s data very well if they were tested at different times or places (or even by different machines).
This means that some people will get rejected more often than others because their measurements don’t match up perfectly with those who have already been approved by the system before them; this can lead to discrimination against certain groups who are already disadvantaged in society due to factors like race/ethnicity and gender identity/expression. In this article, we’ll delve into the different types of biometric identification technologies and how they work.
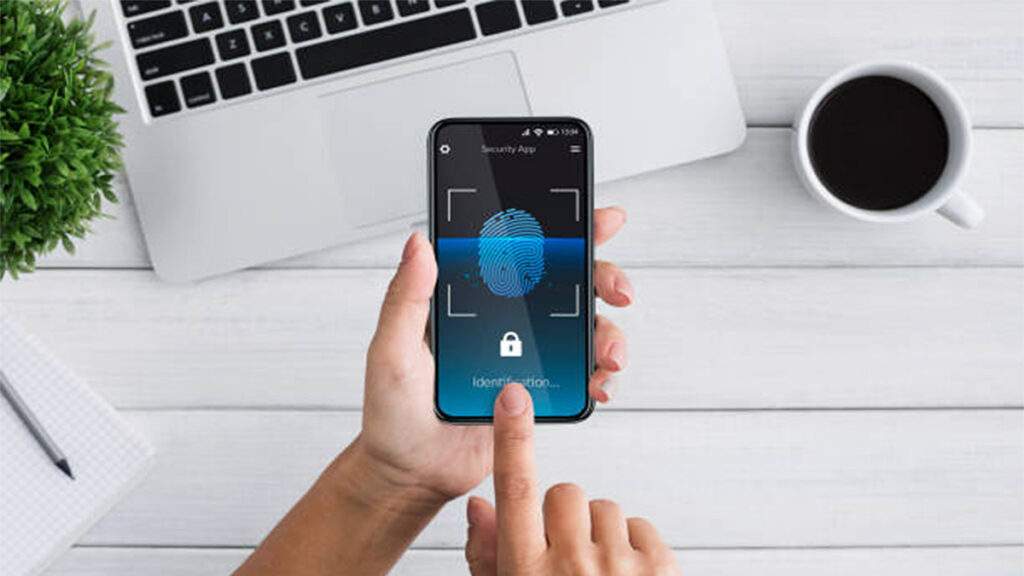
Fingerprint recognition
Fingerprint recognition is the most common form of biometric identification. It involves capturing a digital image of a person’s fingerprint and using that information to identify or verify the person’s identity. Fingerprint recognition technology is used in a variety of applications, including access control systems, time and attendance tracking, and forensic investigations.
Face recognition
Face recognition technology involves capturing a digital image of a person’s face and using it to identify or verify their identity. It’s becoming increasingly popular in areas such as border control, where it’s used to quickly and accurately identify travelers, and in security systems, where it’s used to grant or deny access to restricted areas.
Iris recognition
Iris recognition technology uses unique patterns in a person’s iris to identify or verify their identity. Unlike fingerprint and face recognition, iris recognition technology can be used from a distance, making it a convenient option for security applications.
Voice recognition
Voice recognition technology involves capturing a recording of a person’s voice and using it to identify or verify their identity. It’s becoming increasingly popular as a way of verifying identities over the phone, especially in financial transactions where security is of the utmost importance.
Hand geometry recognition
Hand geometry recognition technology involves capturing a digital image of a person’s hand and using its unique geometry to identify or verify their identity. It’s often used in access control systems and time and attendance tracking applications.
Signature recognition
Signature recognition technology involves capturing a digital image of a person’s signature and using it to identify or verify their identity. It’s often used in financial transactions, where a person’s signature is used as a form of authentication.
Keystroke recognition
Keystroke recognition technology involves analyzing a person’s typing habits and using that information to identify or verify their identity. It’s often used in applications where a password is not enough to ensure secure access, such as online banking or other financial transactions.
Conclusion
Biometric identification technologies are becoming increasingly popular in a variety of applications. They offer a convenient and secure way of verifying a person’s identity and are being used in everything from security systems to financial transactions. As technology continues to advance, it’s likely that we’ll see even more widespread use of biometric identification technologies in the future.
Visit authID for more information about Biometric Identification and Customer Identity Verification.